How I Built a Wazuh Homelab SOC from Scratch
A step-by-step walkthrough of deploying a Wazuh SIEM stack at home — agents, dashboards, alert rules, and what I'd do differently next time.
Read article →
Cyber Security Engineer & SOC Analyst — Melbourne
Melbourne-based cybersecurity & IT professional. CompTIA Security+ certified. Specialising in SOC operations, SIEM, and penetration testing fundamentals. Actively building homelab projects to bridge the experience gap. Open to entry-level cybersecurity, IT roles, and internships.
I'm a cybersecurity & IT professional based in Melbourne, Australia, with a background in Information Systems Management and hands-on security training. I completed Monash University's intensive 6-month cybersecurity bootcamp and earned CompTIA Security+ certification in January 2025.
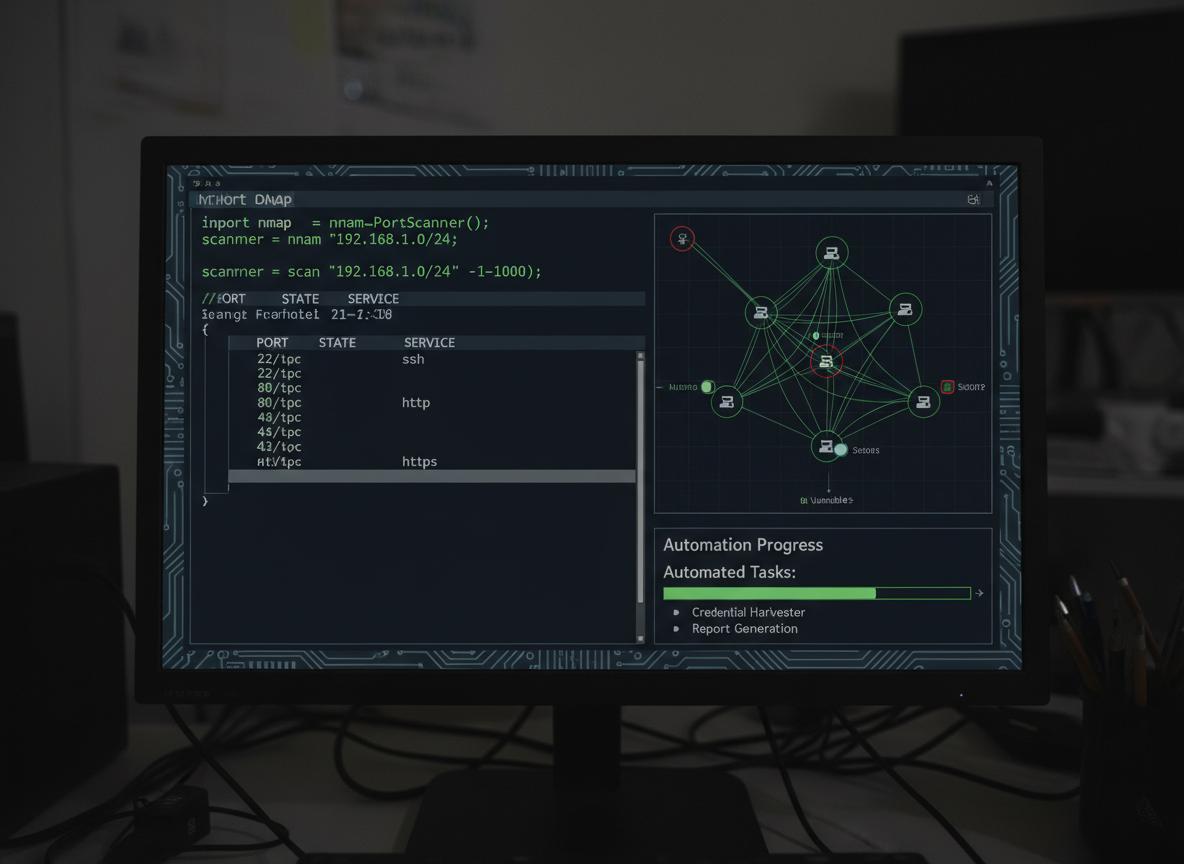
My practical skills span SIEM operations with Splunk & Wazuh, network reconnaissance, digital forensics, and incident response. To bridge the experience gap, I'm extensively building homelab projects — deploying real security tools in virtual environments to develop production-level skills.
Open to entry-level cybersecurity roles, entry-level IT roles, and internships where I can contribute from day one and grow within a team.
Built through the Monash cybersecurity bootcamp, CompTIA Security+, and hands-on project work.
Hands-on simulations, lab builds, and tools — from SOC defence to penetration testing.
Built a full SOC simulation in VMware with Wazuh 4.x SIEM, active agent deployment on Kali Linux, real-time alerting from port scans and SSH brute-force, custom XML detection rules mapped to MITRE ATT&CK, and dashboard visualisation via OpenSearch. Includes automated attack simulation scripts and 50+ screenshots of each phase.
Built an isolated multi-VM homelab using VirtualBox with Kali Linux (attacker), Ubuntu Server (target), and Windows 10 (endpoint). Configured host-only networking and practised reconnaissance, exploitation, SOC workflows, log analysis, and host hardening in a safe air-gapped environment.
 Blue Team
Blue Team
Simulated a SOC analyst role defending web and Windows servers under active attack. Detected privilege escalations and service anomalies, applied Blue Team methodologies, and mapped findings to MITRE ATT&CK tactics in structured IR documentation.
 SIEM
SIEM
Used Splunk Enterprise to detect and analyse simulated DDoS, brute-force, and vulnerability scan events. Built custom dashboards, saved searches, and threshold-based alerts. Correlated Nessus output with Apache logs to surface active threat vectors.
 Recon
Recon
Designed a Python CLI tool to automate network reconnaissance using Nmap. Integrated target scanning, open port identification, and structured result export — replicating the initial enumeration phase of a professional penetration test workflow.
 Forensics
Forensics
Conducted forensic examination of an iPhone in a simulated theft and fraud scenario. Recovered deleted messages, browser history, and geolocation artifacts. Produced an activity timeline with full chain-of-custody documentation per legal admissibility standards.
 Offensive
Offensive
Demonstrated brute-force and dictionary-based password cracking using Hashcat with Python and Bash automation. Presented findings at the bootcamp's final conference, highlighting the real-world implications of weak password policies.
Click any card to view the full credential.
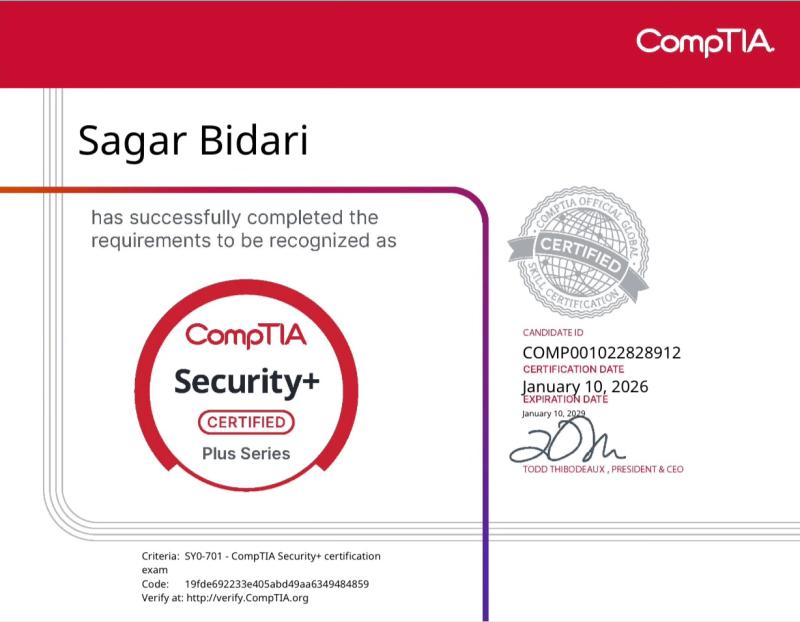
Foundational credential covering network security, cryptography, incident response, and compliance. Key validator for entry-level security roles.

6-month intensive training in SIEM, network security, ethical hacking, vulnerability assessment, and penetration testing fundamentals.

Microskill certification delivered in association with TAFE, Macquarie University, UTS, and Microsoft.
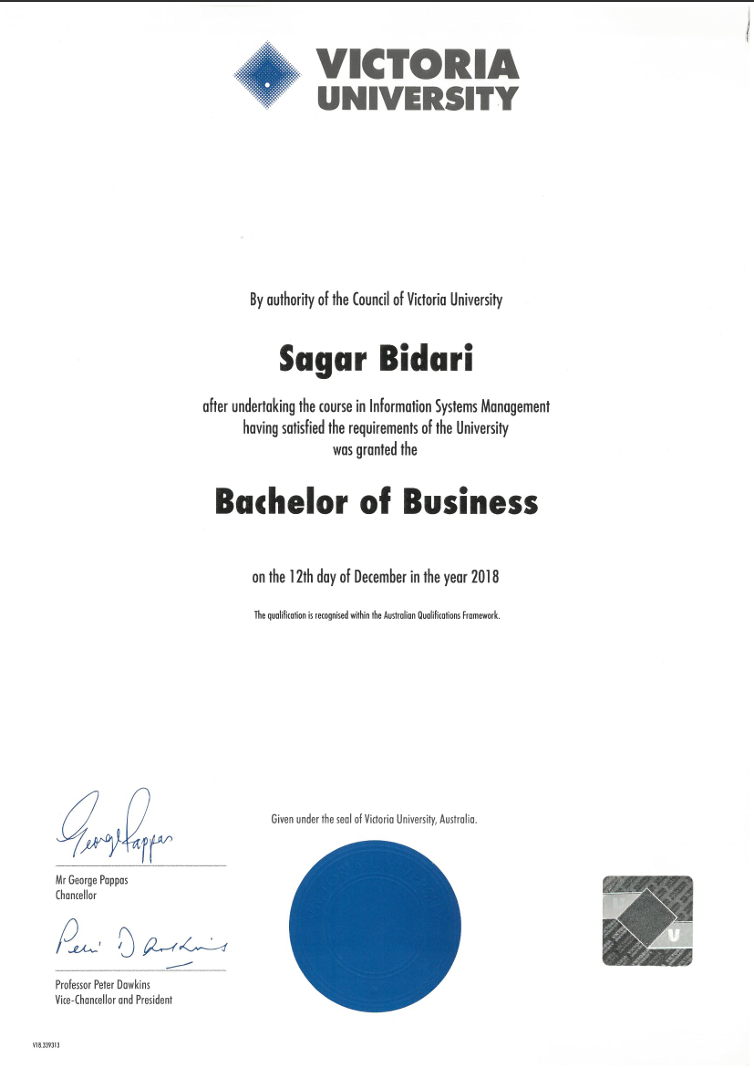
Degree in Information Systems Management covering systems analysis, database design, and IT project leadership.
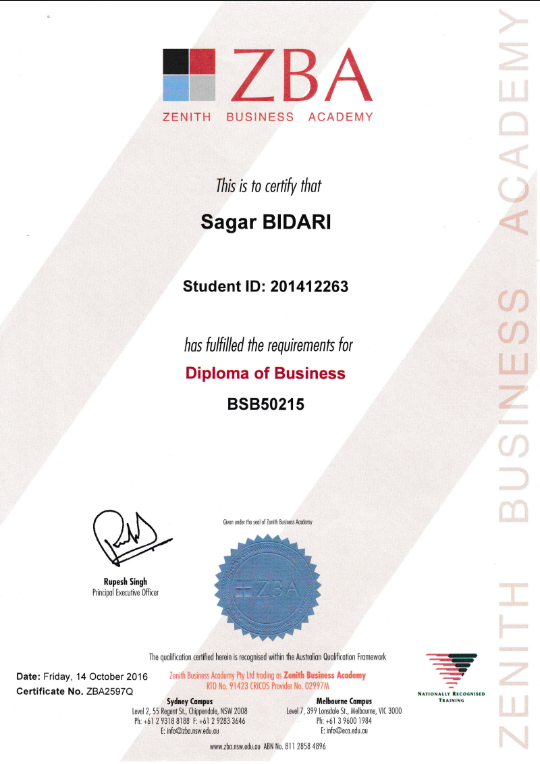
Diploma in business operations and management fundamentals.

Certificate IV (BSB40507) focusing on administrative and operational business skills.
Practical cybersecurity write-ups from real homelab work, cert study, and entry-level career navigation.
A step-by-step walkthrough of deploying a Wazuh SIEM stack at home — agents, dashboards, alert rules, and what I'd do differently next time.
Read article →My realistic 10-week study plan, the resources that actually helped, and what surprised me most about the exam — written for Australian students.
Read article →What I learned building the Vandalay Industries SIEM scenario — SPL queries, alert creation, and how to think like a threat hunter from day one.
Read article →The real path: which certs employers actually check, where Melbourne cybersecurity jobs are posted, and how to stand out with zero work experience.
Read article →How I scripted Nmap to auto-scan, parse XML output, and flag open ports across a lab network — with the full code and explanation.
Read article →Key artefacts, tools like Autopsy and FTK Imager, and the acquisition methods I used in my mobile forensics project — explained for beginners.
Read article →Running Hashcat against captured hashes in a lab environment — attack modes, wordlists, and why this experiment changed how I think about password policies.
Read article →My full VirtualBox multi-VM setup — network segmentation, snapshots, and running attack-and-defence scenarios safely on a budget laptop.
Read article →No IT job history, no degree in CS — here is the exact sequence of certs, projects, and platforms I used to build a credible cybersecurity profile from zero.
Read article →Wazuh, Splunk Free, Wireshark, TheHive, and MISP — what each one does, why it matters for interviews, and how to get hands-on in under an hour.
Read article →Open to entry-level cybersecurity roles, entry-level IT roles, and internships in Melbourne. Currently building homelab projects to demonstrate real skills. If you're hiring or want to connect, reach out — I reply promptly.